Phishing Simulation
The phishing simulation component of Do-Phish serves as a strategic tool to proactively strengthen an organization’s cybersecurity framework by addressing one of the most common vulnerabilities: human error. It also provides a comprehensive awareness assessment, allowing organizations to evaluate and enhance employee resilience against phishing threats.
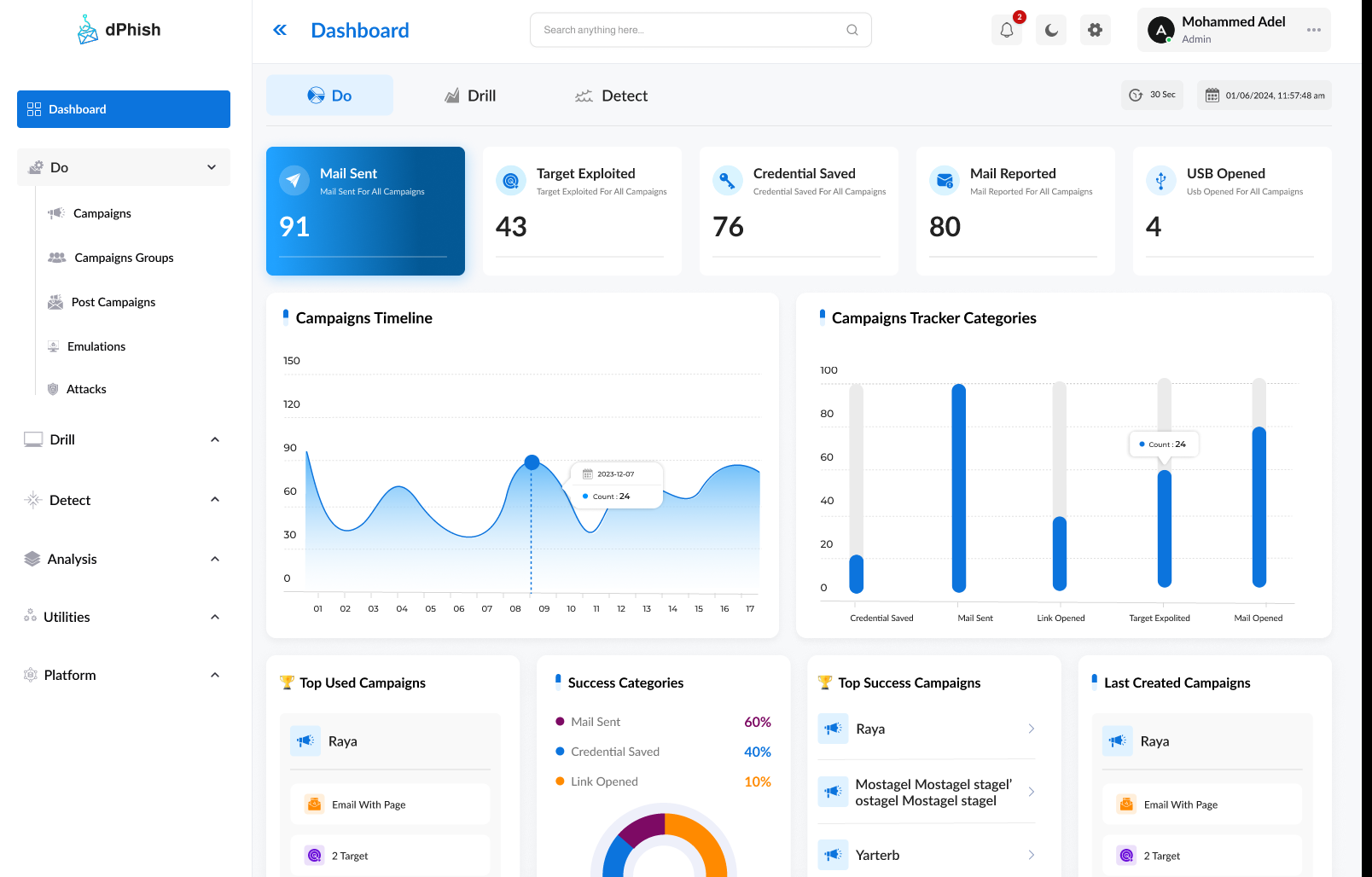
Campaign Preparation
Easily design, customize, and execute sophisticated phishing campaigns.
Multi-Channel Campaigns
Campaign Tracking
Monitor and analyze every interaction with precision.
Detailed activity tracking
Track user-specific data